WP: How to achieve 400 UPH with Locus Fast Pick
WP: How to achieve 400 UPH with Locus Fast Pick Download Now!

Information security is a significant, and growing, concern for organizations, especially those that outsource key business operations to third-party vendors such as Robots-as-a-Service (RaaS), Software-as-a-Service (SaaS), and cloud-computing providers. Information security is a valid concern as mishandled data and insecure processes can leave an organization vulnerable and introduce attacks, such as ransomware and other malware or data theft? 
When you’re outsourcing a critical business process, it’s critical to know you can trust in a vendor’s security practices. One method is to review that vendor's Service Organization Control 2 report, which is more commonly known as a SOC 2 report.
A SOC 2 report is a voluntary compliance standard and auditing procedure for companies with cloud-based products. A SOC2 report assures current and potential customers and stakeholders that a particular service is being provided securely. The American Institute of Certified Public Accountants (AICPA) sets the SOC 2 compliance guidelines to ensure services are secure, available, and confidential.
Benefits of a SOC2 Report in Robotics
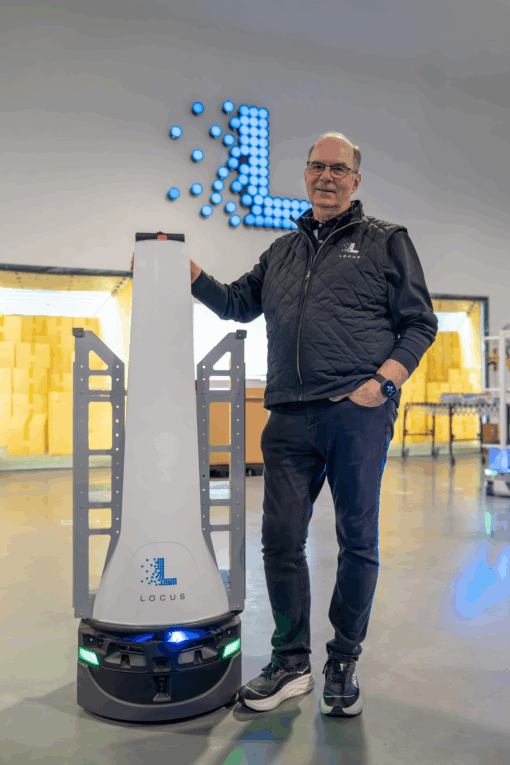
Robotics companies, such as Locus Robotics, must enable a customer to deal with security issues and comply with security, privacy, safety and other regulatory requirements.
Robotics is a relatively new industry, and the industry is changing at a rapid pace. Because of this, standard industry security practices are still being determined and implemented, while few companies have their security practices up and running.
Security practices are the norm for companies with laptops, since they can collect and contain proprietary data. Robots also collect data and need the appropriate security precautions.
During a SOC 2 Type II audit, an independent audit firm is brought in to evaluate current company security practices, including for laptops and robots, against AICPA guidelines.
Audit testing includes a review of the following categories:
- Segregation of Duties
- Change Management
- User Access
- Vulnerability Scanning
- Business Continuity and Disaster Recovery
- Data Backup and Restoration
- Third-Party Management
- Patch Management
These processes are crucial to ensuring security standards are up to par, and a company is SOC 2 compliant.
In summary, robotics is a highly advanced, continuously changing technology. Without effective IT General Controls (ITGC), robotics companies will not maintain a secure and effective compliance posture, so showing SOC 2 compliance is crucial.
What comes next?
SOC 2 compliance is not simply a one-time report. Instead, being able to say that a company is SOC 2 compliant requires continuous compliance and ongoing security practices. Locus Robotics has recently completed its first SOC 2 report and will renew the report annually. We continually monitor compliance effectiveness across the company and update our policies and procedures as necessary. Our SOC 2 report is just one milestone of future achievements.
Click here to read our public-facing SOC 3 report. (Note: A SOC 2 report is private, while the public version of the same report is known as a SOC 3.)
We are dedicated to the continuous review of information security practices, which means making ongoing improvements and updates to maximize the protection of our products and our customers. Check out our TRUST Center to learn more about our ongoing security and compliance reviews, certifications, policies, and best practices.