Locus Robotics Acquires Nexera Robotics: The Next Era of Autonomous Fulfillment Starts Here.
Locus Robotics Acquires Nexera Robotics: The Next Era of Autonomous Fulfillment Starts Here. — Learn More
Understanding the Cybersecurity Risks of GenAI in the Logistics World
Fouad Khalil, Sr. Dir., Ent. Security, Risk & Compliance

As the digital age progresses, logistics managers are increasingly turning to generative artificial intelligence (GenAI) to streamline operations, boost productivity, and enhance decision-making processes. The integration of GenAI into warehouse robotics and systems represents a monumental shift in how inventory is managed, orders are processed, and overall logistics efficiencies are achieved. However, this technological advancement also introduces new cybersecurity challenges that must be meticulously addressed. There are many benefits and cybersecurity risks of GenAI in the logistics world, along with strategies to mitigate these risks.
Embracing GenAI in Warehouses
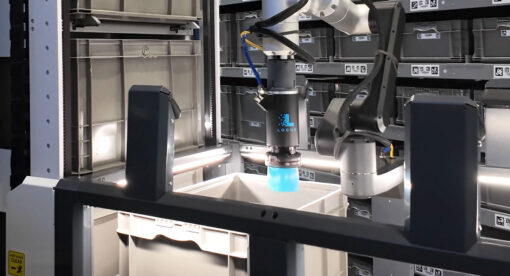
GenAI, with its capability to learn from existing data and generate new, predictive content, is revolutionizing logistics and warehouse operations. From predictive analytics for inventory management to optimizing robots' paths for picking and packing, the potential of GenAI is boundless. Imagine a system that not only forecasts demand based on historical data but also adapts to real-time changes in the market, ensuring that your warehouse is always ahead of the curve. This is the promise of GenAI — a dynamic, intelligent system that evolves with your warehouse needs.
The Cybersecurity Implications
With great power comes great responsibility, and the adoption of GenAI is no exception. Integrating these systems into warehouse operations opens up new vulnerabilities and potential attack vectors for cybercriminals. The data that powers GenAI — often sensitive and proprietary — can become a target. Moreover, the interconnected nature of modern warehouses means a breach in one area can have cascading effects throughout the entire operation.
Uncovering the Risks
The cybersecurity risks associated with GenAI in warehouses can be broadly categorized into data breaches, system vulnerabilities, and compliance challenges:
- Data Breaches: The lifeblood of GenAI is data. A breach could expose sensitive information about inventory, supplier details, and customer data, leading to significant financial and reputational damage.
- System Vulnerabilities: GenAI systems, especially those connected to the internet or external networks, can be exploited by cybercriminals to gain unauthorized access to warehouse operations.
- Compliance Challenges: Warehouses operate under stringent regulatory frameworks concerning data protection and privacy. The use of GenAI must comply with these regulations, or businesses risk hefty fines and legal complications.
Mitigating Cybersecurity Risks
The cybersecurity challenges of integrating GenAI into warehouse operations are significant, but they are not insurmountable. With a proactive approach to cybersecurity, warehouses can harness the power of GenAI while safeguarding their operations against potential threats. Here are strategies to consider:
- Comprehensive Risk Assessment: Begin with a thorough assessment of the cybersecurity risks associated with implementing GenAI. Understand where vulnerabilities may exist and how they can be exploited.
- Robust Data Protection Measures: Implement state-of-the-art encryption, access controls, and data anonymization techniques to protect sensitive information from unauthorized access.
- Regular System Updates and Patch Management: Keep all systems, including AI algorithms and connected devices, updated with the latest security patches to close any vulnerabilities that could be exploited by attackers.
- Employee Training and Awareness: Educate your workforce about the potential cybersecurity risks and best practices for preventing breaches. A well-informed team is your first line of defense against cyber threats.
- Incident Response Plan: Develop a comprehensive incident response plan that outlines steps to be taken in the event of a cybersecurity breach. This should include procedures for containing the breach, assessing the damage, and communicating with stakeholders.
- Collaboration with AI Vendors: Work closely with your GenAI vendors to ensure they adhere to rigorous cybersecurity standards. Understand their data handling and storage practices, and ensure they align with your security requirements.
The Future of Logistics
The integration of GenAI into logistics and warehouse operations is not a question of if but when. As warehouses continue to evolve into smarter, more efficient entities, the role of GenAI will only grow. By embracing this technology while rigorously addressing the cybersecurity challenges it presents, warehouse managers can lead their operations into a new era of productivity and security.
In conclusion, GenAI offers warehouse managers an unprecedented opportunity to optimize operations, enhance efficiency, and stay ahead of market demands. However, the cybersecurity risks associated with this technology cannot be overlooked. By understanding these risks and implementing robust mitigation strategies, warehouses can leverage GenAI to its full potential while ensuring their operations remain secure and compliant. The future of warehousing is bright, and with careful planning and proactive cybersecurity measures, businesses can navigate this new landscape with confidence.
To find out more about our stance on GenAI and cybersecurity, please visit our Trust Center.
About the Author
As Senior Director, Compliance at Locus Robotics, Fouad is responsible for internal and external compliance programs, auditor education, alignment with industry best practices and cross-functional support. He brings extensive experience in the technology space with more than 25 years spanning disciplines in software development, IT support, program and project management and most recently IT Security and Compliance management. Khalil’s career path in technology has provided him with keen insights in the areas of network, system and database administration, software programming, system, software and GUI design, project and product development, solution implementation and much more. For nearly the past two decades, Khalil has focused on data security, security investigations, cybersecurity, security training and awareness, and security compliance– serving as an industry expert in key areas such as IT, NIST, Internal Controls over financial reporting, Sarbanes-Oxley, GDPR, CCPA, PCI DSS, HIPAA and HITECH. Khalil holds a Bachelor’s degree in Electrical and Computer Engineering from Marquette University and CISA, CDPSE and ITIL Foundations certifications. Additionally, he is an active member/contributor in ISACA, IIA and Infragard.