Live Event Series: See real-world automation in action.
Live Event Series: See real-world automation in action. — Learn More
Why Continuous Risk Management is Crucial for Data
Fouad Khalil, Sr. Dir., Ent. Security, Risk & Compliance

If security, compliance and risk professionals were asked to name the most important consideration for their warehouse operations, there is a strong chance they’ll say “the data.” Data is crucial for supporting warehouse customers, pursuing new markets, and a major factor in security and regulatory requirements.
As warehouses continue to grow, expand globally, and increase customer base — data growth and proliferation is tightly aligned with such life cycle activities.
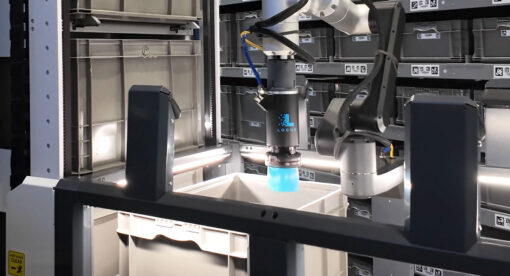
One relatively new business model that incorporates a very big data component with significant data concerns involves Robots-as-a-Service (RaaS). RaaS has become an integral part of warehouse operations and introduces excellent benefits to warehouses and fulfillment centers. Retail and eCommerce rely heavily on RaaS to meet deadlines, improve productivity, and optimize warehouse labor by making workers’ daily jobs more efficient.
The security of data and the technology used with that data is critical, and it needs to be ongoing instead of checking in on it every so often. As I like to say, security, compliance and risk management is NOT a point-in-time.
Let’s take a look at the three factors that make up continuous risk management: compliance, risk mitigation, and security.
Continuous compliance to laws and regulations
First, you need continuous compliance to laws and regulations to ensure your data is protected and compliant throughout the life cycle. These regulations can include GDPR, CCPA, and SOC2, depending on the type of data you manage or process. Regulations and standards at local, state, and government levels are continuously changing and, in some cases, becoming more stringent. The compliance box you checked yesterday may not be applicable today. Ensuring continuous alignment ensures continuous compliance.
Continuous risk management practices
Next, you must adopt continuous risk mitigation practices, such as detective tools, third-party services, and in-house proactive assessments, to ensure ongoing protection and control implementations. Risk management must be part of every function, every product, every service, and all internal processes. The risk landscape is forever changing since businesses always evolve. As we expand to new locations, increase workforce, deploy new solutions, etc. we introduce new risks or elevate existing risks. Risk management must be part of our business-as-usual processes and procedures to ensure companies become proactive rather than reactive.
Continuous security and vigilance
All these best practices, data protection, risk mitigations, and control implementations build the foundation to have better data security. Continuous security happens when we integrate best practices in all business-as-usual activities, assess risk with everything that we do, and align with laws and regulations.
Environments continuously change, products continuously evolve, workforce continuously grow, risk landscape continuously change, and regulations continuously become more stringent. So, what was deployed last month, or pushed to the cloud last week, or upgraded yesterday might have changed as of today.
In point-in-time compliance, security and risk management will not work unless we adopt continuous best practices.
About the Author
As Senior Director, Compliance at Locus Robotics, Fouad is responsible for internal and external compliance programs, auditor education, alignment with industry best practices and cross-functional support. He brings extensive experience in the technology space with more than 25 years spanning disciplines in software development, IT support, program and project management and most recently IT Security and Compliance management. Khalil’s career path in technology has provided him with keen insights in the areas of network, system and database administration, software programming, system, software and GUI design, project and product development, solution implementation and much more. For nearly the past two decades, Khalil has focused on data security, security investigations, cybersecurity, security training and awareness, and security compliance– serving as an industry expert in key areas such as IT, NIST, Internal Controls over financial reporting, Sarbanes-Oxley, GDPR, CCPA, PCI DSS, HIPAA and HITECH. Khalil holds a Bachelor’s degree in Electrical and Computer Engineering from Marquette University and CISA, CDPSE and ITIL Foundations certifications. Additionally, he is an active member/contributor in ISACA, IIA and Infragard.